Loading HoneyMesh...
Loading HoneyMesh...
HoneyMesh is documented publicly with a deliberate boundary: enough detail for operators and buyers to understand the system, without publishing the internal logic an attacker would use to profile or evade it.
HoneyMesh is designed to protect infrastructure without exposing its internal defensive logic in public-facing materials. Public documentation focuses on product outcomes, operator trust boundaries, and privacy guarantees rather than implementation detail.
That means this site intentionally avoids publishing exact detection criteria, trap behavior, internal thresholds, and other low-level mechanics that could help an attacker adapt around the platform.
Community
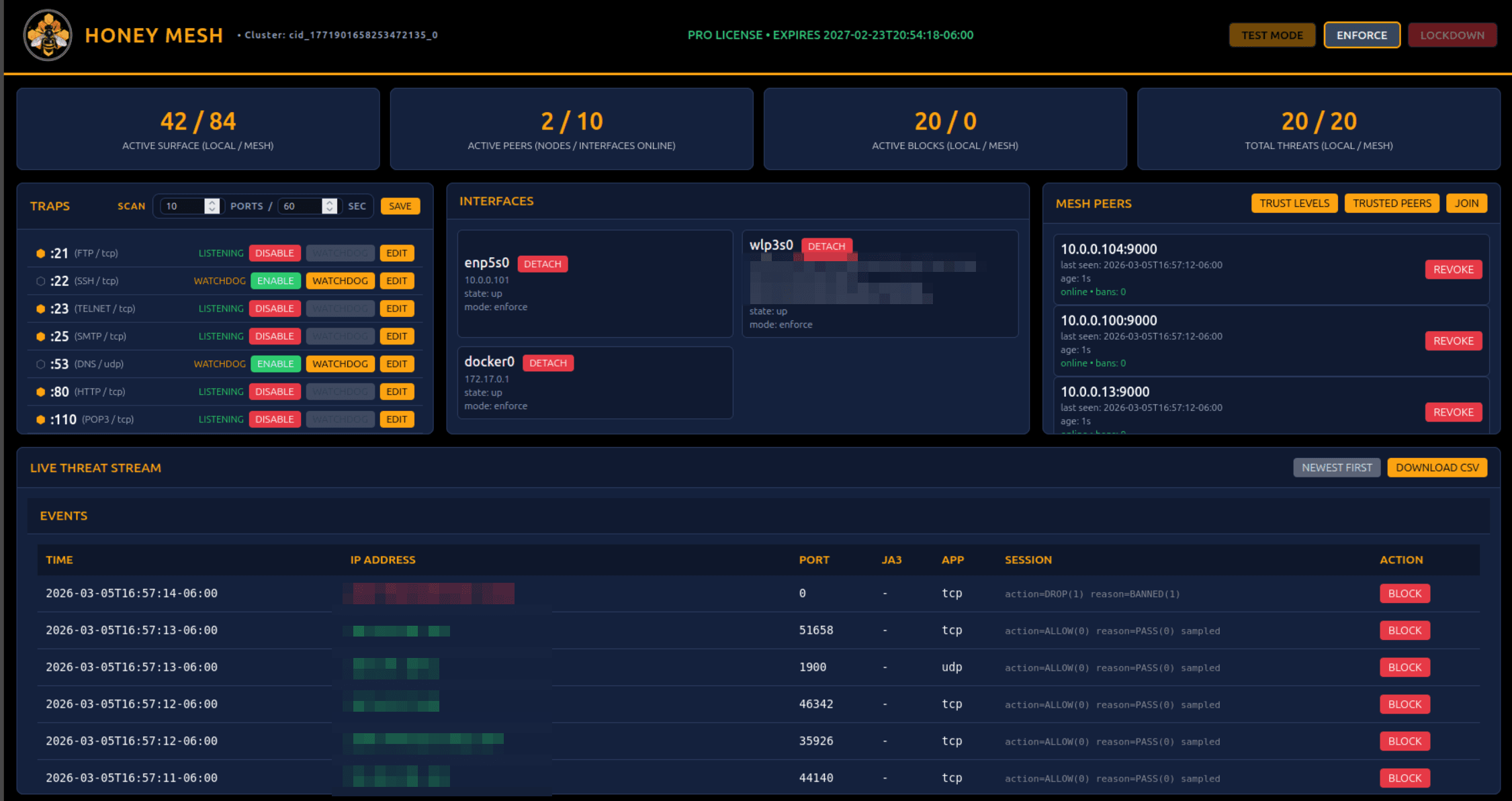
The free Community edition focuses on local protection. Operators can deploy HoneyMesh, view local activity, and protect individual systems without joining any outside sharing workflow.
HoneyMesh Pro
Pro adds premium controls and the option to participate in Trusted Network Sharing. The upgrade is about coordination, visibility, and broader protection across connected environments.
Trusted Sharing & Mesh
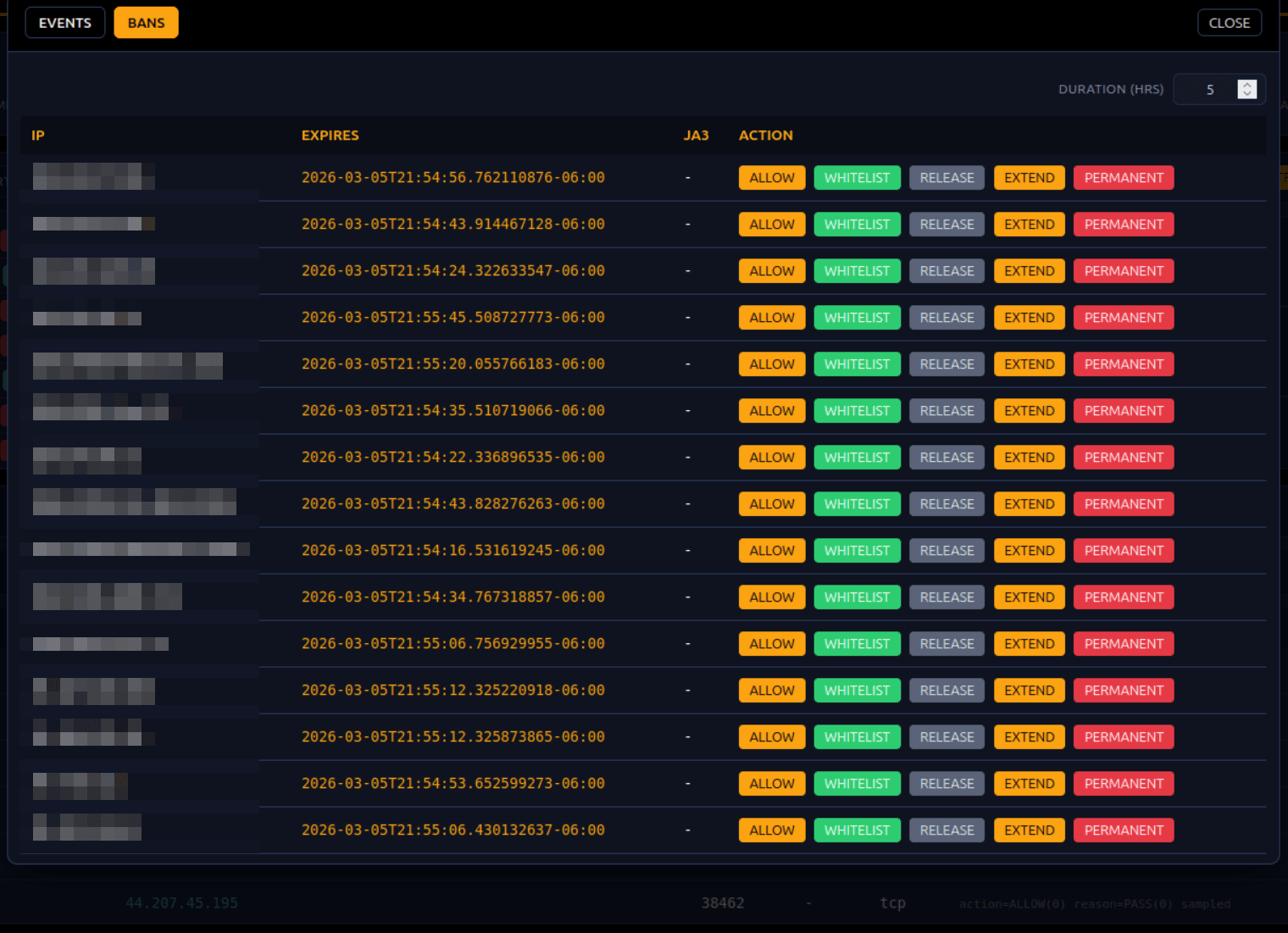
Trusted sharing and trusted mesh participation are available through the HoneyMesh app for Pro deployments. Operators review peer identity, control what is shared, and decide when another network should be allowed to influence local action.
The split is simple: Community is for local protection, Pro adds coordinated intelligence and premium controls, and any sharing or mesh participation stays an explicit operator choice inside the HoneyMesh app.
HoneyMesh does not share your data. It shares minimal, sanitized indicators derived from threats that were already blocked or validated, so trusted participants can recognize similar activity without exposing sensitive content.
HoneyMesh combines local observation, high-speed protection, and optional network coordination. The endpoint is still the place where protection happens. The network adds context and reach, but it does not remove local control.
For operators, the important distinction is simple: local HoneyMesh protects individual systems, while Pro can add trusted sharing, peer review, and sanitized indicator distribution across connected environments.
HoneyMesh Operator Manual
Installation, deployment workflow, licensing model, and operator guidance.
Trusted Sharing Manual
Sharing controls, trust boundaries, node linking, and admin workflows.
Architecture Overview
High-level platform design and product boundaries.
Downloads
Community packages, manuals, licensing disclosures, and audit artifacts.